Communications
This dataset was created for the following paper: Seonghoon Jeong, Boosun Jeon, Boheung Chung, and Huy Kang Kim, "Convolutional neural network-based intrusion detection system for AVTP streams in automotive Ethernet-based networks," Vehicular Communications, DOI: 10.1016/j.vehcom.2021.100338.
- Categories:
 4680 Views
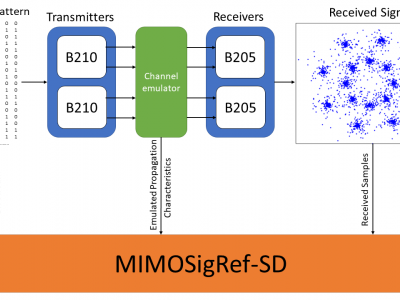
4680 ViewsThe MIMOSigRef-SD dataset was created with the goal to support the research community in the design and development of novel multiple-input multiple-ouotput (MIMO) transceiver architectures. It was recorded using software radios as transmitters and receivers, and a wireless channel emulator to facilitate a realistic representation of a variety of different channel environments and conditions.
- Categories:
 1968 Views
1968 ViewsAccurate and efficient anomaly detection is a key enabler for the cognitive management of optical networks, but traditional anomaly detection algorithms are computationally complex and do not scale well with the amount of monitoring data. Therefore, this dataset enables research on new optical spectrum anomaly detection schemes that exploit computer vision and deep unsupervised learning to perform optical network monitoring relying only on constellation diagrams of received signals.
- Categories:
 1282 Views
1282 Views
Bluetooth communication is widely adopted in IoMT devices due to its various benefits. Nevertheless, because of its simplicity as a personal wireless communication protocol, Bluetooth lacks the security mechanisms which may result in devastating outcomes for patients treated using wireless medical devices.
- Categories:
 1531 Views
1531 ViewsThis dataset is in support of my following Research papers
Preprint (Make sure you have read Caution) :
- Novel ß Transtibial Prosthetic 9-DoF Artificial Leg Adaptive Controller - Part I*
- Categories:
 2193 Views
2193 Views
The prototype transmitter was placed on the floating platform for generating the inductive magnetic field, and the distance between the rotating magnet and the sea surface is 35 cm to 45 cm. The waterproof ferrite-rod coil was hung in the seawater as a receiving antenna at a depth of 10 m.
- Categories:
 170 Views
170 Views
This is DMRS data sets.
- Categories:
 333 Views
333 Views
This repository hosts the data and code for studying the UAV positioning problem under obstructive environment. This study focuses on the scenario of the low-altitude UAV to ground communication in a dense urban environment. There could be a lot of local structure, such as buildings and trees, that blocks the communication signal. As a result, the UAV should be optimized to smartly explore a good propagation condition to communicate with the user. At the same time, the UAV also needs to balance the communication link with the BS.
- Categories:
 445 Views
445 ViewsThis dataset contains RF signals from drone remote controllers (RCs) of different makes and models. The RF signals transmitted by the drone RCs to communicate with the drones are intercepted and recorded by a passive RF surveillance system, which consists of a high-frequency oscilloscope, directional grid antenna, and low-noise power amplifier. The drones were idle during the data capture process. All the drone RCs transmit signals in the 2.4 GHz band. There are 17 drone RCs from eight different manufacturers and ~1000 RF signals per drone RC, each spanning a duration of 0.25 ms.
- Categories:
 18796 Views
18796 Views