Communications

Exact BER Analysis for Two-user NOMA uUing QAM with Arbitrary Modulation Order
- Categories:
 730 Views
730 Views
There has been extensive modelling of the optical wireless channel, and the optimum modulation scheme for a particular channel is well-understood. However, this modelling has not taken into account the trade-offs that transmitter and receiver selection usually involve. For a particular type of transmitter, the modulation bandwidth and available power are closely related, as are receiver bandwidth, active area and sensitivity. In this paper, we present a design approach that takes this device selection into account.
- Categories:
 226 Views
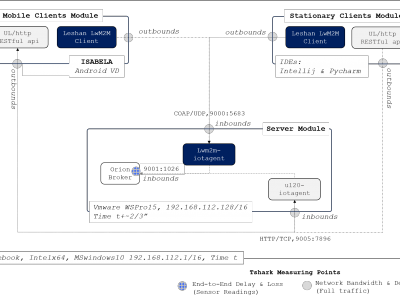
226 ViewsOne-way delay (OWD) is the transmission time of the network packet from the first to the last bit from the sender node to the receiver node. The data set presented here was obtained as a result of measurements performed for the paper “Improving the Accuracy of One-Way Delay Measurements”.
One-way delay measurements were performed using three different utilities:
* the utility from the OWAMP protocol;
* first version of our utility, owping1; and
* the new version of our utility, owping2.
- Categories:
 1194 Views
1194 Views
The following data set is modelled after the implementers’ test data in 3GPP TS 33.501 “Security architecture and procedures for 5G System” with the same terminology. The data set corresponds to SUCI (Subscription Concealed Identifier) computation in the 5G UE (User Equipment) for IMSI (International Mobile Subscriber Identity) based SUPI (Subscription Permanent Identifier) and ECIES Profile A.
- Categories:
 7621 Views
7621 Views
Secure cryptographic protocols are indispensable for modern communication systems. It is realized through an encryption process in cryptography. In quantum cryptography, Quantum Key Distribution (QKD) is a widely popular quantum communication scheme that enables two parties to establish a shared secret key that can be used to encrypt and decrypt messages.
- Categories:
 169 Views
169 Views
The MGWO and GWO code
- Categories:
 218 Views
218 Views
Reconsructed images (video sequences) and results for the paper: "Adaptive block compressive sensing for distributed video coding"
- Categories:
 137 Views
137 Views
The dataset includes 2 parts: private and public traffic.
The private traffic is self-captured network traffic of serveral softwares, such as YouTube, Skype, streaming video, totally 16 categories.
The public traffic is an open VPN dataset, including numorous VPN or nonVPN network services, totally 24 categories.
- Categories:
 1197 Views
1197 Views