Computational Intelligence

New capabilities involving sensors, data collection, and data analysis have enabled innovations in how engineered systems are monitored and maintained. Whereas each new evolution of maintenance philosophies has relied upon the current technological state, this research examines potential future capabilities in the field of prognostics and health management (PHM). PHM algorithms for predicting the estimated time to failure for a system are based on sensor data, physical models, or a combination of both.
- Categories:
 70 Views
70 Views
These datasets are gathered from an array of four gas sensors to be used for the odor detection and recognition system. The smell inspector Kit IX-16 used to create the dataset. each of 4 sensor has 16 channels of readings. Odors of different 12 samples are taken from these six sensors
1- Natural Air
2- Fresh Onion
3- Fresh Garlic
4- Black Lemon
5- Tomato
6- Petrol
7- Gasoline
8- Coffee
9- Orange
10- Colonia Perfume
- Categories:
 483 Views
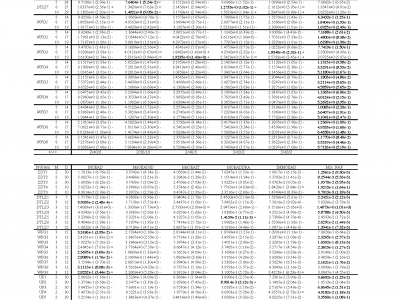
483 ViewsThis is a test dataset for comparison with the latest multi-objective evolutionary algorithms. We have split the experiment into two groups in high and low dimensions respectively, and the experimental results are outstanding. We used IGD as the performance metric, and the data in parentheses are the std of 20 independent repetitions of the experiment and were analyzed for significance.
- Categories:
 72 Views
72 Views
The capabilities of the millimeter wave (mmWave) spectrum to fulfill the ultra high data rate demands of V2X (Vehicle-to-Everything) communications necessitates the need for accurate channel modeling to facilitate the efficient development of next-generation network and device design strategies. Ergo, this work describes the design of a novel fully autonomous robotic beam-steering platform, equipped with a custom broadband sliding correlator channel sounder, for 28GHz V2X propagation modeling activities on the NSF POWDER experimental testbed.
- Categories:
 301 Views
301 Views
CT RECIST response, as measured by the change of tumor diameter, can accurately reflect objective response rate for advanced NSCLC patients. However, there exists obvious discordant between CT RECIST response and prognostic indicators. Thus, our study aimed to identify a new CT RECIST response indicator at the early treatment stage to reflect the prognosis more accurately.We studied 916 tumor lesions obtained through deep learning and found that the shape of the lesions was irregular.
- Categories:
 126 Views
126 Views
We utilized Digital Ocean's cloud service, setting up three Linux virtual machines, each with 1vCPU, 1GB of memory, and a 10GB disk. The architecture included an API gateway for routing requests to a stateless application service backed by a database for storing application data. The application operates the service under a fluctuating workload generated by a load-testing script to simulate real-world usage scenarios. The target source or the application service is integrated with Prometheus, a monitoring tool for gathering system metrics.
- Categories:
 576 Views
576 Views
The update of Android OS constantly brings users various new features and enhances system security. On the other hand, the system and API modifications with the update may introduce the app compatibility issue. The app's SDK version may not align with the Android OS version, making apps not work adequately. This condition will inevitably damage the Android ecosystem. Thus, while developing Android OS, Google considered and deployed compatibility support. The software engineering research community also noticed the Android compatibility issue and conducted some investigations.
- Categories:
 130 Views
130 ViewsSwarm intelligent algorithms have the ability to quickly find optimal solutions to problems, but they suffer from an imbalance between global exploration and local exploitation. The dung beetle optimization (DBO) algorithm was newly developed in 2022 and has excellent comprehensive performance; however, it still suffers from this problem.
- Categories:
 217 Views
217 Views
<p>Time-of-use (ToU) tariffs flexibly offer cheaper electricity prices to industrial and residential users during off-peak periods, encouraging them to shift their peak electricity demands in valley periods. Flow Shop Scheduling (FSS) model is one of the most prevalent models in manufacturing. To explore the significant role of ToU tariffs in manufacturing, this study addresses a novel bi-objective FSS problem under ToU tariffs.</p>
- Categories:
 51 Views
51 Views
In the domain of Natural Language Processing (NLP), the English Writing Fluency Improvement for non-native speakers, particularly in academic contexts, poses significant challenges. While Sentence-level Revision (SentRev) endeavors to address this concern, the existing evaluation corpus, SMITH, falls short in offering a robust and comprehensive assessment of the task. To bridge this gap, our research offers a novel evaluation corpus generation scheme, leading to the creation of Ten-Country Non-native Academic English Corpus (TCNAEC).
- Categories:
 61 Views
61 Views