Security

This dataset contains a list of popular websites and their privacy statements. The websites belong to the three largest South Asian economies, namely, India, Pakistan, and Bangladesh. Each website is categorized into 10 sectors, namely, e-commerce, finance/banking, education, healthcare, news, government, telecom, buy and sell, job/freelance, blogging/discussion. We hope that this dataset will help researchers in investigating website privacy compliance.
- Categories:
 175 Views
175 ViewsWe build an original dataset of thermal videos and images that simulate illegal movements around the border and in protected areas and are designed for training machines and deep learning models. The videos are recorded in areas around the forest, at night, in different weather conditions – in the clear weather, in the rain, and in the fog, and with people in different body positions (upright, hunched) and movement speeds (regu- lar walking, running) at different ranges from the camera.
- Categories:
 11567 Views
11567 Views
Presented here is a dataset used for our SCADA cybersecurity research. The dataset was built using our SCADA system testbed described in our paper below [*]. The purpose of our testbed was to emulate real-world industrial systems closely. It allowed us to carry out realistic cyber-attacks.
- Categories:
 2468 Views
2468 ViewsThis repository contains the results of running more than 70 samples of ransomware, from different families, dating since 2015. It contains the network traffic (DNS and TCP) and the Input/Output (I/O) operations generated by the malware while encrypting a network shared directory. These data are contained in three files for each ransomware sample: one with the information from the DNS requests, other with the TCP connections another one containing the I/O operations. This information can be useful for testing new and old ransomware detection tools and compare their results.
- Categories:
 5745 Views
5745 Views
Five well-known Border Gateway Anomalies (BGP) anomalies:
WannaCrypt, Moscow blackout, Slammer, Nimda, Code Red I, occurred in May 2017, May 2005, January 2003, September 2001, and July 2001, respectively.
The Reseaux IP Europeens (RIPE) BGP update messages are publicly available from the Network Coordination Centre (NCC) and contain:
WannaCrypt, Moscow blackout, Slammer, Nimda, Code Red I, and regular data: https://www.ripe.net/analyse/.
- Categories:
 1400 Views
1400 Views
1. Folder “1.SlibCrypto 4DIAC project” includes 4DIAC (1.10.3) project that can be added into the workspace of 4DIAC. It contains the various standalone applications representing security mechanisms and the extended one shown in Fig. 5.
- Categories:
 221 Views
221 Views
BS-HMS-Dataset is a dataset of the users' brainwave signals and the corresponding hand movement signals from a large number of volunteer participants. The dataset has two parts; (1) Neurosky based Dataset (collected over several months in 2016 from 32 volunteer participants), and (2) Emotiv based Dataset (collected from 27 volunteer participants over several months in 2019).
- Categories:
 4169 Views
4169 Views
Normal
0
false
false
false
EN-US
X-NONE
AR-SA
- Categories:
 810 Views
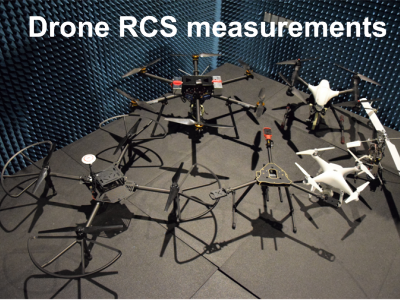
810 ViewsThe dataset contains measurement results of Radar Cross Section of different Unmanned Aerial Vehicles at 26-40 GHz. The measurements have been performed fro quasi-monostatic case (when the transmitter and receiver are spatially co-located) in the anechoic chamber. The data shows how radio waves are scattered by different UAVs at the specified frequency range.
- Categories:
 8274 Views
8274 Views