Artificial Intelligence
Brain-Computer Interface (BCI) technology facilitates a direct connection between the brain and external devices by interpreting neural signals. It is critical to have datasets that contain patient's native languages while developing BCI-based solutions for neurological disorders. However, present BCI research lacks appropriate language-specific datasets, particularly for languages such as Telugu, which is spoken by more than 90 million people in India.
- Categories:
 451 Views
451 Views
The dataset1 includes fake&real news propagation networks on Twitter built according to fact-check information and the news retweet graphs were originally extracted by [FakeNewsNet](https://github.com/KaiDMML/FakeNewsNet).The statistics of the dataset is shown below:| Data | #Graphs | #Total Nodes | #Total Edges | #Avg.
- Categories:
 172 Views
172 ViewsThis study investigates the integration of artificial intelligence (AI) to enhance endpoint management solutions. The research explores AI's impact on security, efficiency, and compliance within enterprise environments (R1). Through case studies and empirical analysis, the paper highlights the benefits and challenges of such integrations, offering insights into future developments.
- Categories:
 4403 Views
4403 Views
This dataset comprises three degrees of freedom (3 DOF) sensory data and simulation data collected from a Kinova robotic arm. The sensory data includes real-time measurements from the robotic arm’s joint positions, velocities, and torques, providing a detailed account of the arm’s dynamic behavior. The dataset also includes simulated data generated using a high-fidelity physics engine, accurately modeling the Kinova arm’s kinematics and dynamics under various operational scenarios.
- Categories:
 139 Views
139 Views
This dataset has been meticulously curated to evaluate the efficiency of Retrieval-Augmented Generation (RAG) pipelines in both retrieval and generative accuracy, with a particular focus on scenarios involving overlapping contexts. The dataset comprises two primary components: Motor data and Employee data. The Motor dataset includes master data of various motor models along with their corresponding manuals, linked by the motor's model name. Similarly, the Employee dataset encompasses employee master data and associated policy documents, linked by department.
- Categories:
 599 Views
599 Views
This dataset is designed for the reconstruction of images of underground potato tubers using received signal strength (RSS) measurements collected by a ZigBee wireless sensor network. It includes RSS data from sensing areas of various sizes, environments with different layouts, and soils with varying moisture levels. The measurements were obtained from 9 potato tubers of differing sizes and shapes, which were buried in two distinct positions within the sensing area.
- Categories:
 235 Views
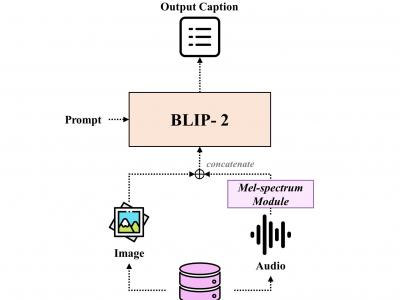
235 ViewsWe construct the triple-modality dataset, VGG-sound+, comprising image-text-audio data. Based on VGG-sound, VGG-sound+ consists of 200,000 audio-visual data entries categorized as video data, including metadata label- ing the category of each video clip. We define the image-text-audio triplet modalities of VGG-sound+ as the dataset Di = (Ii , Ti , Ai), where Ii represents an image snap- shot of the video, Ti denotes a textual description of the video, and Ai signifies the audio clip.
- Categories:
 716 Views
716 Views
In this paper, two datasets for text classification were primarily used in the experiments: AG News and IMDB. The AG News dataset is a widely used four-class news dataset, including four categories: World News, Sports News, Business News, and Technology News. The dataset contains a total of 120,000 samples, with 114,000 samples in the training set and the remaining 6,000 samples in the test set. The IMDB dataset is a movie review dataset used for sentiment analysis, primarily for binary classification tasks, i.e., positive and negative reviews.
- Categories:
 82 Views
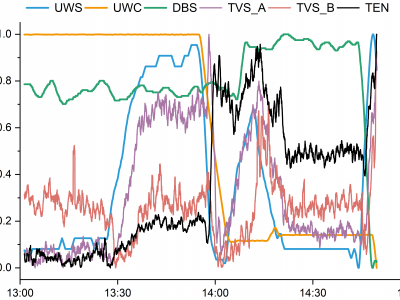
82 ViewsThis graph illustrates the visualization trend of a subset of the dataset I have uploaded, which comprises 6500*9 data points. The dataset consists of nine columns representing underwater speed (UWS), underwater course (UWC), depth below the surface (DBS), rate of change in speed (RCS), rate of change in course (RCC), rate of change in depth (RCD), trend A and B of vibrational signals (TVS_A, TVS_B) and electromagnetic noise trend (TEN) recorded by the AUV.
- Categories:
 140 Views
140 Views