*.csv
Distributed Denial of Service (DDoS) attacks first appeared in the mid-1990s, as attacks stopping legitimate users from accessing specific services available on the Internet. A DDoS attack attempts to exhaust the resources of the victim to crash or suspend its services. Time series modeling will help system administrators for better planning of resource allocation to defend against DDoS attacks. Different Time Series analysis techniques are applied to detect the DDoS attacks.
- Categories:
 6329 Views
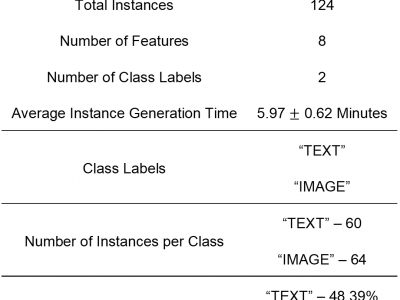
6329 ViewsHuman intention is an internal, mental characterization for acquiring desired information. From
interactive interfaces, containing either textual or graphical information, intention to perceive desired
information is subjective and strongly connected with eye gaze. In this work, we determine such intention by
analyzing real-time eye gaze data with a low-cost regular webcam. We extracted unique features (e.g.,
Fixation Count, Eye Movement Ratio) from the eye gaze data of 31 participants to generate the dataset
- Categories:
 637 Views
637 Views
The data has been collected using direct questionnaires from the patients of Sylhet Diabetes Hospital in Sylhet, Bangladesh and approved by a doctor.
This dataset is available in UCI Machine Learning Repository.
- Categories:
 4954 Views
4954 Views
Any work using this dataset should cite the following paper:
- Categories:
 9771 Views
9771 Views
Dataset contains generated traffic from single requests towards DNS and DNS over Encryption servers as well as network traffic generated by browsers towards multiple DNS over HTTPS servers. The dataset contains also logs and csv files with queried domains. The IP addresses of the DoH servers are provided in the readme so that users can easily label the data extracted from pcap files. The dataset may be used for Machine Learning purposes (DNS over HTTPS identification).
- Categories:
 1244 Views
1244 ViewsThe Firearm Recoil Dataset was collected utilizing a wrist worn accelerometer to record the recoil generated from one subject’s use of 15 different firearms of the Handgun, Rifle and Shotgun class. The type of the firearm based on its ability to auto-load or not is also denoted.
- Categories:
 889 Views
889 Views
We elaborate on the dataset collected from our testbed developed at Washington University in St. Louis, to perform real-world IIoT operations, carrying out attacks that are more prelevant against IIoT systems. This dataset is to be utilized in the research of AI/ML based security solutions to tackle the intrusion problem.
- Categories:
 2887 Views
2887 Views
This dataset includes the rotor geometry image (*.png) and motor parameters (*.csv) of interior permanent magnet synchronous motors. The rotor geometry covers three structures: 2D-, V-, and Nabla-structures. The motor parameters are generated by machine learning based on the finite element analysis results. The software JMAG Designer 19.1 was used for the finite element analysis.
- Categories:
 1975 Views
1975 Views