Communications

The file contains the S4 data for 340GHz wave through the clear air. The data are obtained by a experimental setup working at 340 GHz, and the wave propagates throug the outdoor atmosphere, and the measured data are processed to the scintillation index data S4, the meteorogical data are given, too. The meteorogical data includes temperature with the unit of ℃,the water vapour density in unit of g/m3, and the wind speed in unit of m/s. the S4 data is in the last row in the dataset.
- Categories:
 49 Views
49 ViewsThe Internet Graphs (IGraphs) dataset is a substantial collection of real intra-AS (Autonomous System) graphs sourced from the Internet Topology Data Kit (ITDK) project. Comprising a total of 90,326 graphs, each ranging from 12 to 250 nodes, this dataset provides a diverse and extensive resource for the exploration and analysis of network structures within autonomous systems.
- Categories:
 920 Views
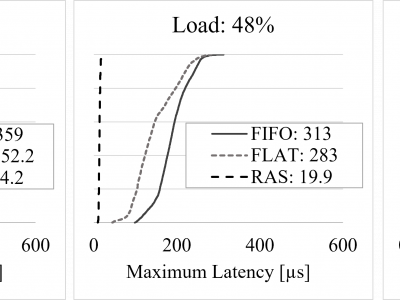
920 ViewsThe data set was used to produce three figures (Figs. 4, 5, and 6) in the experimental section of a manuscript submitted for review to the IEEE Communications Magazine. The submission, titled Lightweight Determinism in Large-Scale Networks, describes a novel approach to the realization of network determinism in packet-switched networks of generic size and topology.
- Categories:
 403 Views
403 ViewsThe data repository includes simulation parameters and results for the Quantum Approximate Optimization Algorithm (QAOA) channel decoding applied to short block-lengths in Additive White Gaussian Noise (AWGN) channels. This research utilizes a Random Linear Code (RLC) in a Coded Modulation (CM) design at the encoder. Extensive simulations were conducted using IBM Quantum Lab and the ibmq_qasm_simulator back-end provided by IBM Quantum, simulating quantum circuits on classical hardware.
- Categories:
 126 Views
126 ViewsThe Transport-level pAcket RouTing ANalysis Tool for Cloud-native Applications (TARTAN) Dataset contains TARTAN/HiPerConTracer Traceroute runs between an endpoint in Oslo, Norway and the public Comprehensive TeX Archive Network (CTAN, https://www.ctan.org) and Comprehensive R Archive Network (CRAN, https://cran.r-project.org) mirror we
- Categories:
 417 Views
417 ViewsIn this dataset, 4 radio channel measurements at 28 GHz are presented. These have been captured in two different spots of a highway with a fixed Tx and a mobile Rx onboard a car, emulating a V2I link. The Tx was placed both on the roadside (3 measurement runs) and on an overpass (1 measurement). Each run consists of around 4.29 s of continuously captured channel impulse responses (CIRs), with a channel sampling period of 65 μs and a delay resolution of 2 ns.
- Categories:
 313 Views
313 ViewsThe rapid evolution of communication networks and the ever-increasing demand for efficient data transfer have led to the development of cognitive networking, which aims to enhance network performance through intelligent and adaptive protocols. To facilitate research and development in this domain, we present a comprehensive dataset detailing the parameters of a Network Protocol Stack which can be used to develop a Cognitive Network Protocol Stack designed for efficient networking.
- Categories:
 1451 Views
1451 Views
The dataset contains 5G positioning measurements simulated using a MATLAB raytracer tool in realistic environments (outdoors and indoors).
Outdoor scenarios include static and dynamic users in the urban area of Città Studi, Milan, Italy, near the Politecnico di Milano - Campus Leonardo.
The indoor context is reconstructed using a LiDAR acquisition in the MADE Competence Center I4.0 located in Politecnico di Milano - Campus Durandò, Bovisa, Milan, Italy.
The datasets include:
- Categories:
 481 Views
481 Views
The datasets consists of the traffic-delay pairs collected in a real network. For each link connecting two switches, we measured the link delay associated with 1000 evenly-divided traffic test points. To obtain the traffic-delay pairs at a traffic test point of a link, the traffic generation machine, connected to the starting switch of the link, firstly sent data packets to the traffic generation machine, connected to the ending switch of the link, at the corresponding rate (i.e., the traffic value of the traffic test point).
- Categories:
 249 Views
249 Views