Security

The data was built in order to evaluate behavior of the Word Error Rate (WER) of the adversaries' and victims' Error Correcting Codes for different symbol error probability (channel errors) is affected by different code parameters for the adversaries' Error Correcting Code.
For the non-binary communication channel with a GRS based covert channel WER of the victims' Error Correcting Code are shifted to the right as the minimal distance of the adversaries' Error Correcting Codes decrease.
- Categories:
 153 Views
153 ViewsThe security of systems with limited resources is essential for deployment and cannot be compromised by other performance metrics such as throughput. Physically Unclonable Functions (PUFs) present a promising, cost-effective solution for various security applications, including IC counterfeiting and lightweight authentication. PUFs, as security blocks, exploit physical variations to extract intrinsic responses based on applied challenges, with Challenge-Response Pairs (CRPs) uniquely defining each device.
- Categories:
 401 Views
401 Views
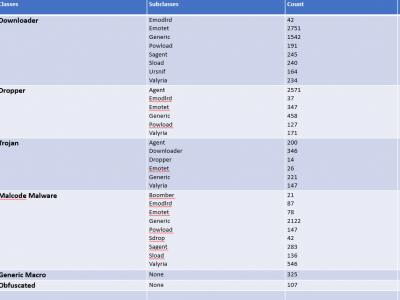
In deep learning, images are utilized due to their rich information content, spatial hierarchies, and translation invariance, rendering them ideal for tasks such as object recognition and classification. The classification of malware using images is an important field for deep learning, especially in cybersecurity. Within this context, the Classified Advanced Persistent Threat Dataset is a thorough collection that has been carefully selected to further this field's study and innovation.
- Categories:
 1859 Views
1859 ViewsMicrosoft contains a productive tool known as MS Office but the inclusion of VBA Macros inside the MS Office for automation purposes makes it a way for attackers to perform malicious activities. To get an up-to-date dataset, the research regarding VBA macros is still working to find efficient ways to detect it. To perform analysis, the dataset is required which is publically harder to find. To overcome this issue, a dataset is created from VirusTotal, VirusShare, Zenodo, Malware Bazaar, Github and InQuest Labs.
- Categories:
 1184 Views
1184 Views
The WPT dataset was specially created for "Web Page Tampering Detection Based on Dynamic Temporal Graph Pre-training" and encompasses over 200,000 regular web pages from 75 websites across the finance, healthcare, and education sectors, in addition to 1,541 tampered examples sourced from zone-h.org. This dataset organizes web pages as nodes and their links as edges within a discrete dynamic graph structure, capturing snapshots at various moments in time. Each node integrates structural, textual, and statistical features into a robust 148-dimensional feature vector for every page.
- Categories:
 70 Views
70 Views
The sudden shift from physical office location to a fully remote or hybrid work model accelerated by the COVID-19 pandemic is a phenomenon that changed how organizations traditionally operated and thereby introduced new vulnerabilities and consequently changed the cyber threat landscape. This has led organizations around the globe to seek new approaches to protect their enterprise network. One such approach is the adoption of the Zero Trust security approach due to its many advantages over the traditional/perimeter security approach.
- Categories:
 615 Views
615 ViewsA Wormhole attack in a dataset, where certain nodes (wormhole nodes) create an illusion of having a shorter path in network communications to attract traffic, the dataset will reflect network traffic patterns altered by these deceptive links. Here’s the structure for 95,000 records:
- Categories:
 385 Views
385 ViewsAn IEEE 802.15.4 backscatter communication dataset for Radio Frequency (RF) fingerprinting purposes.
It includes I/Q samples of transmitted frames from six carrier emitters, including two USRP B210 devices (labeled as c#) and four CC2538 chips (labeled as cc#), alongside ten backscatter tags (identified as tag#). The carrier emitters generate an unmodulated carrier signal, while the backscatter tags employ QPSK modulation within the 2.4 GHz frequency band, adhering to the IEEE 802.15.4 protocol standards.
- Categories:
 461 Views
461 Views