Sinkhole Attack Simulation Dataset
- Citation Author(s):
- Submitted by:
- Muhammad Zunnurain Hussain
- Last updated:
- DOI:
- 10.21227/wg5s-ra72
- Data Format:
 348 views
348 views
- Categories:
- Keywords:
Abstract
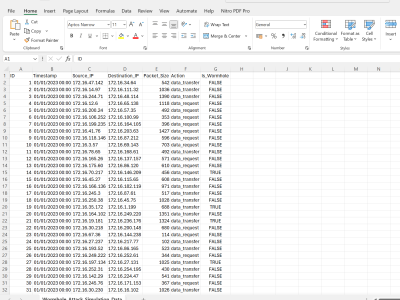
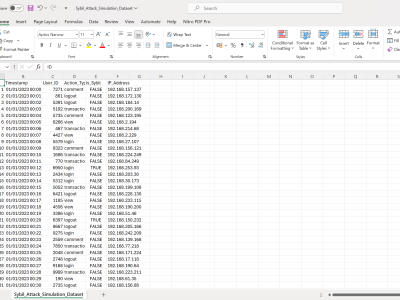
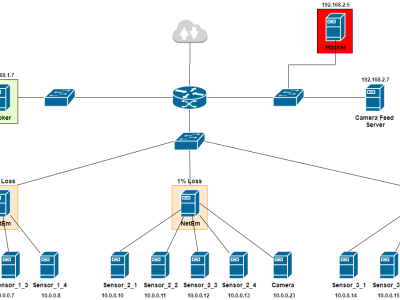
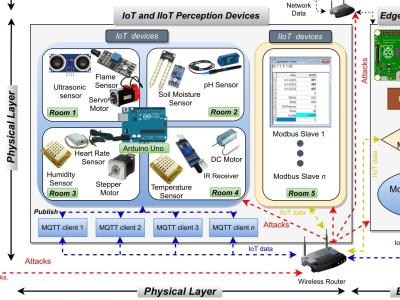
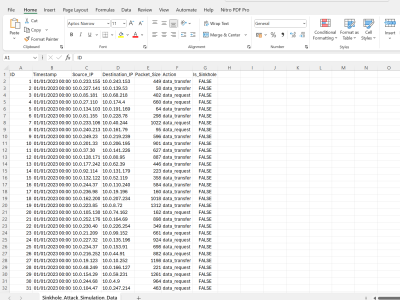
a Sinkhole attack in a dataset, we'll generate data that typically reflects network traffic and interactions, where some nodes act as sinkholes by attracting all or most of the traffic due to malicious intent. Here's how I'll structure the dataset for 80,000 records:
- ID: Unique identifier for each interaction.
- Timestamp: Randomized date and time.
- Source_IP: IP address of the source node.
- Destination_IP: IP address of the destination node, with some IPs recurrently appearing in a sinkhole pattern.
- Packet_Size: Size of the packet sent from source to destination.
- Action: Type of action (e.g., data_request, data_transfer).
- Is_Sinkhole: Indicates if the action was towards a sinkhole node (True or False).
Instructions:
The dataste is in csv format and help researchers doing research in security domain.