Security

This document presents the probability calculation for distinguishing Hamming weight distributions. Given two distinct Hamming weight scenarios (HW = 0 and HW = 1), we derive the probability that an observed value \(x\) originates from the HW = 0 distribution. Utilizing Bayes' theorem, we calculate the conditional probability and provide the final expression for \(P(HW = 0 \mid x)\).
- Categories:
 28 Views
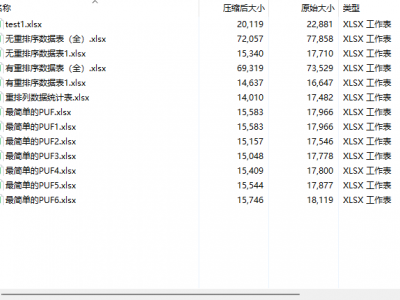
28 ViewsThe dataset is based on PYTHON and machine modeling of 5000 challenge response pairs for both regular CRO PUFs and HMCRO PUFs.This includes the design of reordering schemes
The dataset is based on PYTHON and machine modeling of 5000 challenge response pairs for both regular CRO PUFs and HMCRO PUFs.This includes the design of reordering schemes
The dataset is based on PYTHON and machine modeling of 5000 challenge response pairs for both regular CRO PUFs and HMCRO PUFs.This includes the design of reordering schemes
- Categories:
 147 Views
147 Views
We propose a deep learning-based dataset for smart contract vulnerability detection, combining three public datasets to support and facilitate blockchain security research. This comprehensive dataset includes a variety of common types of smart contract vulnerabilities, such as re-entrancy attacks, integer overflows, and improper access controls.
By consolidating and uniformly annotating the data, we provide detailed vulnerability information and classification tags for each smart contract. The main features and contributions of the dataset are as follows:
- Categories:
 361 Views
361 ViewsThe Unified Multimodal Network Intrusion Detection System (UM-NIDS) dataset is a comprehensive, standardized dataset that integrates network flow data, packet payload information, and contextual features, making it highly suitable for machine learning-based intrusion detection models. This dataset addresses key limitations in existing NIDS datasets, such as inconsistent feature sets and the lack of payload or time-window-based contextual features.
- Categories:
 2512 Views
2512 Views
DALHOUSIE NIMS LAB BENIGN DATASET 2024-2 dataset comprises data captured from Consumer IoT devices, depicting three primary real-life states (Power-up, Idle, and Active) experienced by everyday users. Our setup focuses on capturing realistic data through these states, providing a comprehensive understanding of Consumer IoT devices.
The dataset comprises of nine popular IoT devices namely
Amcrest Camera
Smarter Coffeemaker
Ring Doorbell
Amazon Echodot
Google Nestcam
Google Nestmini
Kasa Powerstrip
- Categories:
 226 Views
226 ViewsThis project aims to generate smart home IoT datasets (especially Zigbee traffic data) in order to support research on smart home IoT network and device profiling, behaviour modelling, characterization, and security analysis. The Zigbee traffic data is captured in a real house with two Zigbee networks containing over 25 Zigbee devices which monitor the daily activities inside the house. The captured Ethernet traffic data from Home Assistant also contains the status data of several non-Zigbee IoT devices such as printers, a smart thermostat, and entertainment devices.
- Categories:
 2252 Views
2252 Views
Smart grid, an application of Internet of Things (IoT) is modern power grid that encompasses power and communication network from generation to utilization. Home Area Network (HAN), Field or Neighborhood Area Network (FAN/NAN) and Wide Area network (NAN) using Wireless LAN and Wireless/Wired WAN protocols are employed from generation to utilization . Advanced Metering Infrastructure, a utilization side infrastructure facilitates communication between smart meters and the server where energy efficient protocols are mandate to support smart grid .
- Categories:
 522 Views
522 ViewsA dataset related to a cable under anomalies conditions while a transmitter (AWG) sends a binary PAM signal to a receiver. The signals are acquired by an oscilloscope. The anomalies were manually forced on the cable under test: air-exposed, water-exposed conductors, and tapping. In the dataset, the signals are also available for normal cable.
- Categories:
 416 Views
416 Views