Cybersecurity

This dataset provides packet traces captured in a realistic 5G Vehicle-to-Everything (5G-V2X) environment, encompassing both legitimate vehicular communications and Distributed Denial of Service (DDoS) attacks. By deploying four user equipments (UEs) under multiple attacker configurations, the collected captures reflect various DDoS types (TCP SYN, UDP, and mixed) and reveal their impact on 5G-V2X networks. The dataset is further enriched with Argus files and CSV feature tables, facilitating data-driven approaches such as Machine Learning (ML)-based detection agents.
- Categories:
 357 Views
357 ViewsThe recent developments in the field of the Internet of Things (IoT) bring alongside them quite a few advantages. Examples include real-time condition monitoring, remote control and operation and sometimes even remote fault remediation. Still, despite bringing invaluable benefits, IoT-enriched entities inherently suffer from security and privacy issues. This is partially due to the utilization of insecure communication protocols such as the Open Charge Point Protocol (OCPP) 1.6. OCPP 1.6 is an application-layer communication protocol used for managing electric vehicle chargers.
- Categories:
 789 Views
789 Views
One of the major challenges of microgrid systems is the lack of comprehensive Intrusion Detection System (IDS) datasets specifically for realistic microgrid systems' communication. To address the unavailability of comprehensive IDS datasets for realistic microgrid systems, this paper presents a UNSW-MG24 dataset based on realistic microgrid testbeds. This dataset contains synthesized benign network traffic from different campus departments, network flow of attack activities, system call traces, and microgrid-specific data from an integrated Festo LabVolt microgrid system.
- Categories:
 300 Views
300 Views
The PermGuard dataset is a carefully crafted Android Malware dataset that maps Android permissions to exploitation techniques, providing valuable insights into how malware can exploit these permissions. It consists of 55,911 benign and 55,911 malware apps, creating a balanced dataset for analysis. APK files were sourced from AndroZoo, including applications scanned between January 1, 2019, and July 1, 2024. A novel construction method extracts Android permissions and links them to exploitation techniques, enabling a deeper understanding of permission misuse.
- Categories:
 675 Views
675 ViewsThis dataset was developed in the context of the NANCY project and it is the output of the experiments involving cyberattacks against services that are running in a 5G coverage expansion scenario. The coverage expansion scenario involves a main operator and a micro-operator which extends the main operator’s coverage and can also provide additional services, such as Artificial Intelligence-based cyberattack detection.
- Categories:
 503 Views
503 Views
The security of Internet of Things (IoT) networks has become a major concern in recent years, as the number of connected objects continues to grow, thereby opening up more potential for malicious attacks. Supervised Machine Learning (ML) algorithms, which require a labeled dataset for training, are increasingly employed to detect attacks in IoT networks. However, existing datasets focus only on specific types of attacks, resulting in ML-based solutions that struggle to generalize effectively.
- Categories:
 387 Views
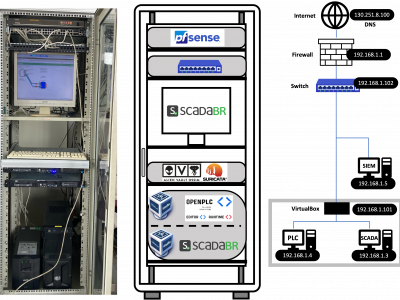
387 ViewsThe increasing integration of cyber-physical systems in industrial environments has under scored the critical need for robust security measures to counteract evolving cyber threats. In response to this need, this work introduces an open-source dataset designed to enhance the development and evaluation of cybersecurity solutions for smart industries. The dataset comprises a traffic capture of an industrial control system (ICS) subjected to a variety of simulated cyber-attacks, including but not limited to denial of service (DoS), man-in-the-middle (MITM), and malware infiltration.
- Categories:
 1522 Views
1522 ViewsSmart grids are nowadays featured by distributed energy resources, both renewables, traditional sources and storage systems. Generally, these components are characterized by different control technologies that interact with the generators through smart inverters. This exposes them to a variety of cyber threats. In this context, there is a need to develop datasets of attacks on these systems, in order to evaluate the risks and allow researchers to develop proper monitoring algorithms.
- Categories:
 898 Views
898 Views
5G Network slicing is one of the key enabling technologies that offer dedicated logical resources to different applications on the same physical network. However, a Denial-of-Service (DoS) or Distributed Denial-of-Service (DDoS) attack can severely damage the performance and functionality of network slices. Furthermore, recent DoS/DDoS attack detection techniques are based on the available data sets which are collected from simulated 5G networks rather than from 5G network slices.
- Categories:
 4888 Views
4888 Views