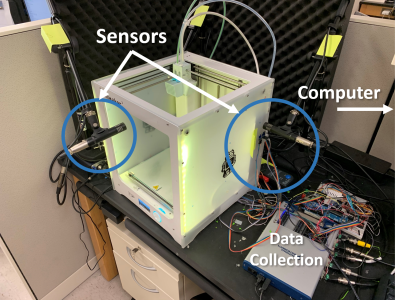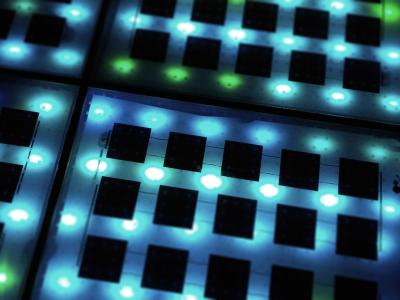
One of the major challenges of microgrid systems is the lack of comprehensive Intrusion Detection System (IDS) datasets specifically for realistic microgrid systems' communication. To address the unavailability of comprehensive IDS datasets for realistic microgrid systems, this paper presents a UNSW-MG24 dataset based on realistic microgrid testbeds. This dataset contains synthesized benign network traffic from different campus departments, network flow of attack activities, system call traces, and microgrid-specific data from an integrated Festo LabVolt microgrid system.
- Categories: