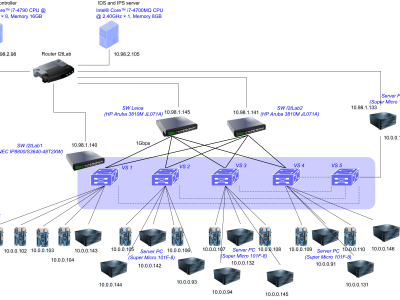
Slow-rate DDoS attacks are recent threats targeting next-generation networks such as IoT, 5G, etc. Unlike conventional high-rate DDoS, slow-rate DDoS have not been deeply studied, mainly due to the limited number of existing datasets with real traces.
- Categories: