DDoS

This dataset provides packet traces captured in a realistic 5G Vehicle-to-Everything (5G-V2X) environment, encompassing both legitimate vehicular communications and Distributed Denial of Service (DDoS) attacks. By deploying four user equipments (UEs) under multiple attacker configurations, the collected captures reflect various DDoS types (TCP SYN, UDP, and mixed) and reveal their impact on 5G-V2X networks. The dataset is further enriched with Argus files and CSV feature tables, facilitating data-driven approaches such as Machine Learning (ML)-based detection agents.
- Categories:
 380 Views
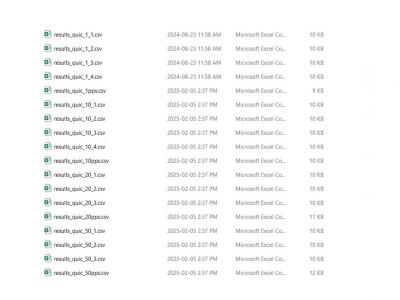
380 ViewsThis dataset contains results and scripts from experiments evaluating the resilience of the QUIC protocol against handshake flooding attacks. It aims to support researchers and developers in analyzing the performance of QUIC against handshake flooding attacks. The experiments utilize three prominent QUIC implementations: aioquic, quic-go, and picoquic, providing a comprehensive comparison of their resilience. Additionally, to benchmark the performance and resilience of QUIC, SYN flood attacks were conducted against TCP with SYN cookies.
- Categories:
 216 Views
216 Views
5G Network slicing is one of the key enabling technologies that offer dedicated logical resources to different applications on the same physical network. However, a Denial-of-Service (DoS) or Distributed Denial-of-Service (DDoS) attack can severely damage the performance and functionality of network slices. Furthermore, recent DoS/DDoS attack detection techniques are based on the available data sets which are collected from simulated 5G networks rather than from 5G network slices.
- Categories:
 4925 Views
4925 ViewsWith the modern day technological advancements and the evolution of Industry 4.0, it is very important to make sure that the problem of Intrusion detection in Cloud , IoT and other modern networking environments is addressed as an immediate concern. It is a fact that Cloud and Cyber Physical Systems are the basis for Industry 4.0. Thus, intrusion detection in cyber physical systems plays a crucial role in Industry 4.0. Here, we provide the an intrusion detection dataset for performance evaluation of machine learning and deep learning based intrusion detection systems.
- Categories:
 4099 Views
4099 Views
Dataset with diverse type of attacks in Programmable Logic Controllers:
1- Denial of Service
- Flooding
- Amplification/Volumetric
2- Man in the Middle
The full documentation of the dataset is available at: https://arxiv.org/abs/2103.09380
- Categories:
 3109 Views
3109 Views
Boğaziçi University DDoS dataset (BOUN DDoS) is generated in Boğaziçi University via Hping3 traffic generator software by flooding TCP SYN, and UDP packets. This dataset includes attack-free user traffic as well as attack traffic and suitable for evaluating network-based DDoS detection methods. Attacks are towards one victim server connected to the backbone router of the campus. Attack packets have randomly generated spoofed source IP addresses. The data-trace was recorded on the backbone and included over 4000 active hosts.
- Categories:
 3236 Views
3236 ViewsThis work intend to identify characteristics in network traffic that are able to distinguish the normal network behavior from denial of service attacks. One way to classify anomalous traffic is the data analysis of the packets header. This dataset contains labeled examples of normal traffic (23.088 instances), TCP Flood attacks (14.988 instances), UDP Flood (6.894 instances), HTTP Flood (347 instances) and HTTP Slow (183 instances) distributed in 73 numeric variables.
- Categories:
 1515 Views
1515 Views