Security

We propose a general framework for using deep learning to detect vulnerabilities, named SySeVR. For evaluate the SySeVR, we collect the Semantics-based Vulnerability Candidate (SeVC) dataset, which contains all kinds of vulnerabilities that are available from the National Vulnerability Database (NVD) and the Software Assurance Reference Dataset (SARD).
- Categories:
 1090 Views
1090 Views
The dataset contains several publicly available Bug Bounty Program policy documents collected from the internet.
These were used to develop the theory of Bug Bounty Program practices.
- Categories:
 224 Views
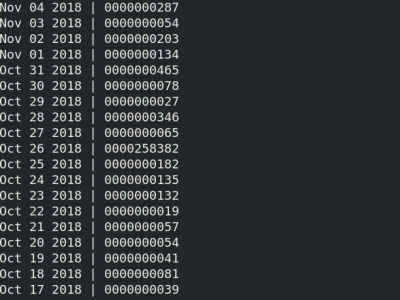
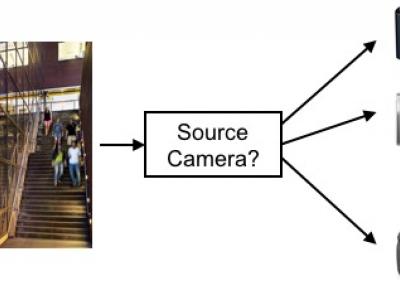
224 ViewsThis database consists of the data used for the 2018 IEEE Signal Processing Cup. This iteration of the Signal Processing Cup was a forensic camera model identification challenge. Teams of undergraduate students were tasked with building a system capable of determining type of camera (manufacturer and model) that captured a digital image without relying on metadata.
- Categories:
 809 Views
809 Views
This dataset is composed of the following benchmarks:
- Categories:
 566 Views
566 Views
Expansion of wireless body area networks (WBANs) applications such as health-care, m-banking, and others has lead to vulnerability of privacy and personal data. An effective and unobtrusive natural method of authentication is therefore a necessity in such applications. Accelerometer-based gait recognition has become an attractive solution, however, continuous sampling of accelerometer data reduces the battery life of wearables. This paper investigates the usage of received signal strength indicator (RSSI) as a source of gait recognition.
- Categories:
 604 Views
604 Views
Static analysis is increasingly used by companies and individual code developers to detect bugs and security vulnerabilities. As programs grow more complex, the analyses have to support new code concepts, frameworks and libraries. However, static-analysis code itself is also prone to bugs. While more complex analyses are written and used in production systems every day, the cost of debugging and fixing them also increases tremendously.
- Categories:
 195 Views
195 Views
Dataset used in paper "Machine Learning Cryptanalysis of a Quantum Random Number Generator" published at IEEE TIFS https://ieeexplore.ieee.org/document/8396276.
- Categories:
 1059 Views
1059 Views
The two dataset files contains the experimental results for ICDB DMode and ICDB AMode.
- Categories:
 259 Views
259 Views