
Anomaly detection is a well-known topic in cybersecurity. Its application to the Internet of Things can lead to suitable protection techniques against problems such as denial of service attacks.
- Categories:

Anomaly detection is a well-known topic in cybersecurity. Its application to the Internet of Things can lead to suitable protection techniques against problems such as denial of service attacks.
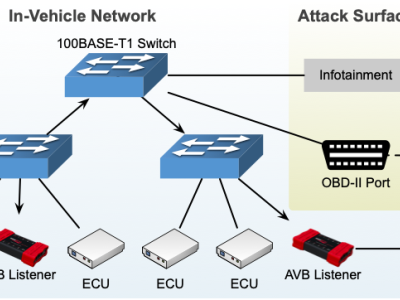
This dataset was created for the following paper: Seonghoon Jeong, Boosun Jeon, Boheung Chung, and Huy Kang Kim, "Convolutional neural network-based intrusion detection system for AVTP streams in automotive Ethernet-based networks," Vehicular Communications, DOI: 10.1016/j.vehcom.2021.100338.

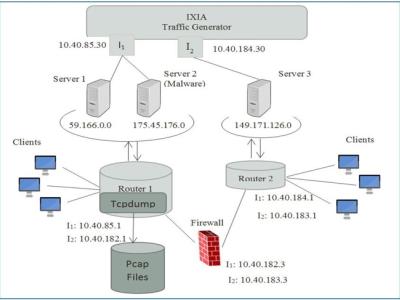
Collecting and analysing heterogeneous data sources from the Internet of Things (IoT) and Industrial IoT (IIoT) are essential for training and validating the fidelity of cybersecurity applications-based machine learning. However, the analysis of those data sources is still a big challenge for reducing high dimensional space and selecting important features and observations from different data sources. The study proposes a new testbed for an IIoT network that was utilised for creating new datasets called TON_IoT that collected Telemetry data, Operating systems data and Network data.
One of the major research challenges in this field is the unavailability of a comprehensive network based data set which can reflect modern network traffic scenarios, vast varieties of low footprint intrusions and depth structured information about the network traffic. Evaluating network intrusion detection systems research efforts, KDD98, KDDCUP99 and NSLKDD benchmark data sets were generated a decade ago. However, numerous current studies showed that for the current network threat environment, these data sets do not inclusively reflect network traffic and modern low footprint attacks.

Dataset contains ten days real-world DNS traffic captured from campus network comprising of 4000 hosts in peak load hours. Dataset also contains labelled features.