Multi-Step Cyber-Attack Dataset (MSCAD for Intrusion Detection)
- Citation Author(s):
-
Mohammad Almseidin (Aqaba University of Technology)Jamil Al-Sawwa (Tafila Technical University)Mouhammd Alkasassbeh (Princess Sumaya University for Technology)
- Submitted by:
- Mohammad Almseidin
- Last updated:
- DOI:
- 10.21227/phr0-e264
- Data Format:
- Research Article Link:
- Links:
 3434 views
3434 views
- Categories:
- Keywords:
Abstract
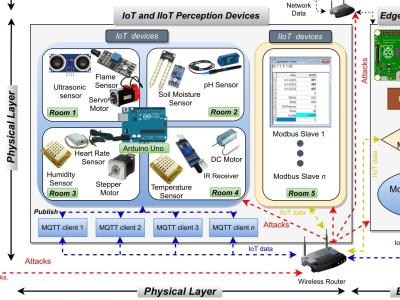
Nowadays, with the rapid increase in the number of applications and networks, the number of cyber multi-step attacks has been increasing exponentially. Thus, the need for a reliable and acceptable Intrusion Detection System (IDS) solution is becoming urgent to protect the networks and devices. However, implementing a robust IDS needs a reliable and up-to-date dataset in order to capture the behaviors of the new types of attacks, especially multi-step attacks. In this work, a new benchmark Multi-Step Cyber-Attack Dataset (MSCAD) is introduced. MSCAD includes two multi-step scenarios; the first scenario is a password cracking attack, and the second attack scenario is a volume-based Distributed Denial of Service (DDoS) attack. The MSCAD was assessed in two manners; firstly, the MSCAD was used to train IDS. Then, the performance of IDS was evaluated in terms of G-mean and Area Under Curve (AUC). Secondly, the MSCAD was compared with other free open-source and public datasets based on the latest key criteria of a dataset evaluation framework. The results show that IDS-based MSCAD achieved the best performance with G-mean of 0.83 and obtained good accuracy to detect the attacks. Besides, the MSCAD successfully passed twelve key criteria.
Instructions:
There are seven files in this dataset: MSCAD.xlsx, N-0, Scan-1, App-01, App-02, W-B-01, W-B-02:
· MSCAD.xlsx: MSCAD.xlsx presents the labeled version of the dataset. The six PCAP files were processed using Wireshark. Throughout the processing, we analyzed the timestamp of the network traffic (malicious and normal traffic) in order to label the network traffic. After processing these PCAP files, the generated dataset (MSCAD) contains 77 features (network parameters) with labels.
· N-0: N-0 presents (Normal traffic).
· Scan-1: Scan-1 presents (Port Scan Traffic [Full, SYN, FIN, and UDP Scan]).
· App-01: App-01 presents (App-based DDoS [HTTP Slowloris DDoS]).
· App-02: App-02 presents (Volume-based DDoS [ICMP Flood]).
· W-B-01: W-B-01 presents (Web Crawling).
· W-B-02: W-B-02 presents (Password Cracking [Brute Force]).
The MSCAD includes two multi-step cyber-attacks scenarios. The two multi-step attack scenarios were performed as follows:
Multi-step Attack Scenario A: In this scenario, an attacker aims to perform a password cracking attack (Brute force) on any host within the victim network. The attacker executes this attack in three main sequential steps. Firstly, the port scan was executed simultaneously. Secondly, the HTTrack Website Copier was used as a website crawler tool to take an offline copy of the web application pages. Using a password list of 47 entries and a user list of 10 entries resulted in 470 attempts to crack the password. Finally, the Brute force script was executed.
· Multi-step Attack Scenario B: In scenario B, the attacker aims to execute the volume-based DDoS on any host within the victim network. The volume-based DDoS was performed based on three sequential steps. The first step of the volume-based DDoS attack is to execute the port scan attack (Full, SYN, FIN, and UDP Scan) simultaneously. Then, the next step is to launch the APP-based DDoS attack using HTTP Slowloris DDoS attack. Finally, executing the volume-based DDoS attack using the Radware tool. This scenario took an hour and three hosts 192.168.159.131, 192.168.159.14, and 192.168.159.16) were infected by the volume-based DDoS attack.



hvjkbjlnkjkn