Detection rate and false alarm rate for Pagoda

- Citation Author(s):
- Submitted by:
- Yulai Xie
- Last updated:
- DOI:
- 10.21227/c3es-rv63
- Data Format:
 179 views
179 views
- Categories:
- Keywords:
Abstract
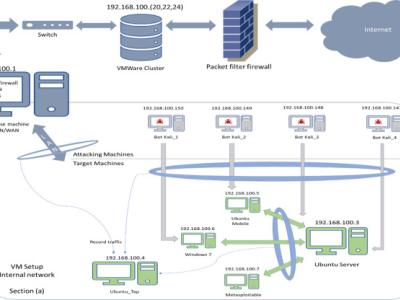
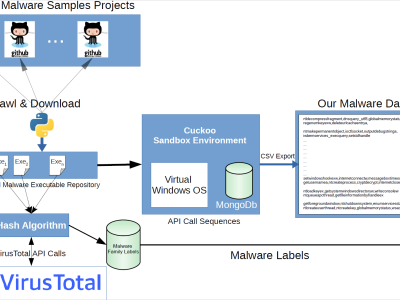
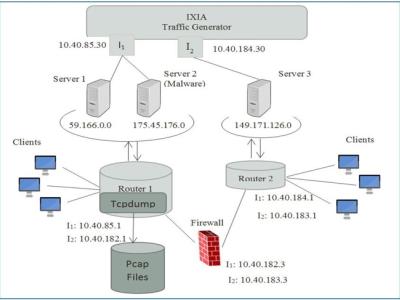
Efficient intrusion detection and analysis of the security landscape in big data environments present challenge for today's users. Intrusion behavior can be described by provenance graphs that record the dependency relationships between intrusion processes and the infected files. Existing intrusion detection methods typically analyze and identify the anomaly either in a single provenance path or the whole provenance graph, neither of which can achieve the benefit on both detection accuracy and detection time. We propose Pagoda, a hybrid approach that takes into account the anomaly degree of both a single provenance path and the whole provenance graph. It can identify intrusion quickly if a serious compromise has been found on one path, and can further improve the detection rate by considering the behavior representation in the whole provenance graph. Pagoda uses a persistent memory database to store provenance and aggregates multiple similar items into one provenance record to maximumly reduce unnecessary I/O during the detection analysis. In addition, it encodes duplicate items in the rule database and filters noise that does not contain intrusion information. The experimental results on a wide variety of real-world applications demonstrate its performance and efficiency.
Instructions:
This file contains all the original test data for detecting intrusion using provenance based intrusion detection that takes into account both a single path and the whole provenance graph. We have added the annotation in the file to make it more easily read.