Browser Based Side-Channel Defenses Datasets
- Citation Author(s):
-
Anatoly ShustermanAyush AgrawalGiorgio MaoneSioli O'ConnellDaniel GenkinYossi OrenYuval Yarom
- Submitted by:
- Anatoly Shusterman
- Last updated:
- DOI:
- 10.21227/f8kk-xq86
- Data Format:
- Links:
 440 views
440 views
- Categories:
Abstract
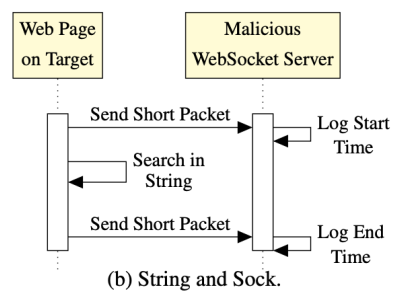
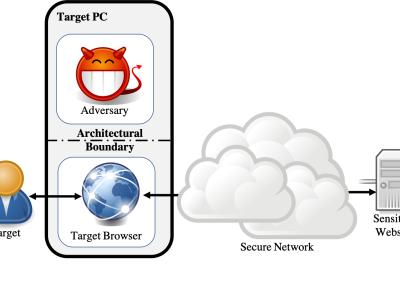
The "eternal war in cache" has reached browsers, with multiple cache-based side-channel attacks and countermeasures being suggested. A common approach for countermeasures is to disable or restrict JavaScript features deemed essential for carrying out attacks.
To assess the effectiveness of this approach, in this work we seek to identify those JavaScript features which are essential for carrying out a cache-based attack. We develop a sequence of attacks with progressively decreasing dependency on JavaScript features, culminating in the first browser-based side-channel attack which is constructed entirely from Cascading Style Sheets (CSS) and HTML, and works even when script execution is completely blocked. We then show that avoiding JavaScript features makes our techniques architecturally agnostic, resulting in microarchitectural website fingerprinting attacks that work across hardware platforms including Intel Core, AMD Ryzen, Samsung Exynos, and Apple M1 architectures.
As a final contribution, we evaluate our techniques in hardened browser environments including the Tor browser, DeterFox (Cao et al., CCS 2017), and Chrome Zero (Schwartz et al., NDSS 2018). We confirm that none of these approaches completely defend against our attacks. We further argue that the protections of Chrome Zero need to be more comprehensively applied, and that the performance and user experience of Chrome Zero will be severely degraded if this approach is taken.
Instructions:
TBD




https://cheese-chompers-3d.org/
Get ready for fast-paced cheese-fueled action in Cheese Chompers 3D, where every rat fights for glory.