Test data for Regulatable Mechanism for Transacting Data Assets
- Citation Author(s):
-
Liutao Zhao
- Submitted by:
- Liutao Zhao
- Last updated:
- DOI:
- 10.21227/skna-kn55
 views
views
- Categories:
Abstract
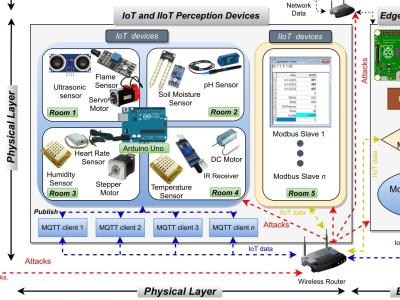
Blockchain technology is widely used in data asset transactions. Especially for the private data of the public, such data cannot be circulated to unauthorized receivers, it is necessary to ensure that the transaction records and data contents can be audited and traced. In this paper, based on bilinear mapping, we construct a triple receiver public key encryption scheme as a regulatable data asset transaction mechanism, and construct a blockchain data asset transaction platform, namely Digital Asset Exchange Protocol. In the triple receiver public key encryption scheme, the sender uses its private key and the public keys of the three receivers to encrypt the message, and then the three receivers can use their private keys to decrypt independently. The above process does not require interaction among participants to realize Diffie-Hellman session key calculation. Through formal proof, we prove that if the gap bilinear Diffie-Hellman problem and the computational Diffie-Hellman problem are difficult, the proposed examples has chosen plaintext attack security and adaptive chosen ciphertext attack security, respectively. In addition, the security reduction of the triple receiver public key encryption scheme is compact and there is no reduction loss. Compared with the duple receiver encryption scheme proposed by Diameter, the proposed scheme has a similar decryption speed, but it adds an important additional function, that is, the sender and the three receivers can decrypt independently. Eventually, evaluations show that the proposed scheme has both decentralized and trust management regulation capabilities, and is suitable for data asset transactions in the IoT.