CAIDA UCSD DDoS 2007 Attack Dataset

- Citation Author(s):
-
Vaishali Shirsath (Vidyavardhinis College Of Engineering and Technology)
- Submitted by:
- Vaishali Shirsath
- Last updated:
- DOI:
- 10.21227/dvp9-s124
- Data Format:
 1584 views
1584 views
- Categories:
- Keywords:
Abstract
Maximum capture length for interface 0: 65000
First timestamp: 1186262976.484933000
Last timestamp: 1186263276.484931000
Unknown encapsulation: 0
IPv4 bytes: 2768247216
IPv4 pkts: 45954067
IPv4 flows: 2860519
Unique IPv4 addresses: 7075
Unique IPv4 source addresses: 7065
Unique IPv4 destination addresses: 7075
Unique IPv4 TCP source ports: 65532
Unique IPv4 TCP destination ports: 847
Unique IPv4 UDP source ports: 2
Unique IPv4 UDP destination ports: 3
Unique IPv4 ICMP type/codes: 24
IPv6 pkts: 0
IPv6 bytes: 0
non-IP protocols: 0
non-IP pkts: 0
Instructions:
The CAIDA "DDoS Attack 2007" Dataset
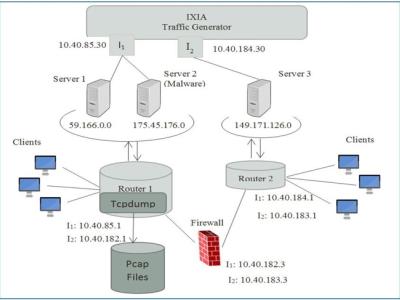
This dataset contains approximately one hour of anonymized traffic
traces from a Distributed Denial-of-Service (DDoS) attack on
August 4, 2007. This type of attack attempts to block access to
the targeted server by consuming computing resources on the server
and by consuming all of the bandwidth of the network connecting
the server to the Internet.
The total size of the dataset is 21 GB and covers about one hour
(20:50:08 UTC to 21:56:16 UTC). The attack starts around 21:13 when
the network load increases rapidly (within a few minutes) from
about 200 kbits/s to about 80 Mbits/s. The one-hour trace is split
up in 5-minute files and stored in pcap format.
The traces include only attack traffic to the victim and responses
from the victim. We have removed, as much as possible, non-attack
traffic. We anonymized the traces using CryptoPAn prefix-preserving
anonymization using a single key. [The original trace was processed with
CoralReef options -Canon=cryptopan,keyfile=<key.txt>, -l4 and -r.]
Subdirectories to-victim and from-victim contain the same trace, with
traffic to the victim (including the attack traffic) in subdirectory
to-victim, and all traffic from the victim (including responses to the
attack) in subdirectory from-victim.
Users can read these traces with any software that reads the pcap
(tcpdump) format, including the CoralReef Software Suite, tcpdump,
Wireshark, and many others.
Acceptable Use Agreement
------------------------
The AUA that you accepted when you were given access to these datas is included
in pdf format as a separate file in the same directory as this README file.
Attribution
-----------
When referencing this dataset (as required by the AUA), please use:
The CAIDA UCSD "DDoS Attack 2007" Dataset
http://www.caida.org/data/passive/ddos-20070804_dataset.xml
Users are encouraged to include the following attribution in the
acknowledgments section of their document:
Support for CAIDA's Internet Traces is provided by the National
Science Foundation, the US Department of Homeland Security,
and CAIDA Members.
Special thanks to the Collaborative Center for Internet
Epidemiology and Defenses (CCIED, "SeaSide") for their assistance
with this dataset.